ASI

AS-i Technology Tutorial
Introduction
In 1990, in Germany, a consortium of successful companies developed a bus system for networks of sensors and actuators, called Actuator Sensor Interface (AS-Interface or in its abbreviated form AS-i).
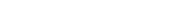
This system emerged to meet some requirements defined from the experience of its founding members and to supply the market whose hierarchical level is bit-oriented. In this way, the AS-i network was conceived to complement the other systems and make the connections between sensors and actuators with their respective controllers simpler and faster.
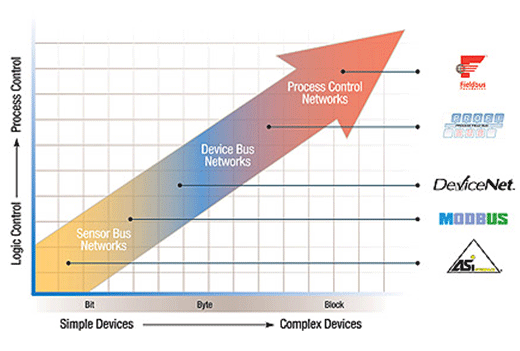
Figure 1.1: Technological Scenarios - Source: ATAIDE, F.H. (2004)
AS-i associations
The AS-International Association or AS-Interface UK Expert Alliance is a user group founded in 1991 by companies and users of the AS-InterfaceÒ system. The group's goal is to make AS-i a world standard in the bit-oriented field level of industrial automation, within the Sensor Bus category.
The group provides its members with the latest market and technology information, including technical information support, product certification, activities, courses, fairs and other events. More information at http://www.as-interface.net or http://www.as-interface.com.
As of 1999 the AS-i network has been standardized by the standard EN 50295/IEC 62026-2 and the associations that regulate AS-International Association (2008) (www.as-interface.net) or AS-Interface UK Expert Alliance (www .as-interface.com) are open to new members who want to develop certified products.
benefits
An industrial system formed by AS-i networks is considered the most economical and ideal for communication between actuators and sensors. The benefits of using an AS-i network range from hardware savings to commissioning an AS-i network itself.
Figure 3.1 illustrates some factors that must be considered when choosing an industrial network and the benefits to each of them when using AS-i networks.
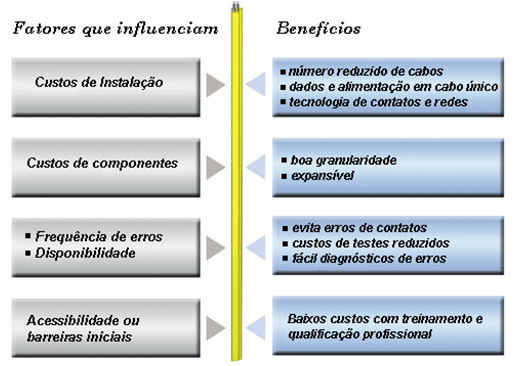
Figure 3.1: Analysis in the choice of industrial network.
Source: AS-International Association (2008)
This approach leads us to summarize these benefits as follows.
Simplicity
An AS-i network is very simple, as it only requires a single cable to connect input and output modules from any manufacturers. Users of an AS-i network do not need to have in-depth knowledge of industrial systems or communication protocols. Unlike other digital networks, the AS-i network does not need terminators and equipment description files. Simplicity is its strong point.
Performance
AS-i systems are efficient and incredibly fast, making them able to replace large and expensive systems. There are AS-i masters specially designed to communicate with legacy control systems and promote a smooth integration between existing technologies. Best of all, this is done simply and reliably.
Flexibility
Expandability is a snap – just plug in a module, address it, then plug in the network cable. Make sure the power LED is on and then you are ready to connect the next module. The AS-i network supports any cabling topology: star, bus, tree, ring or any other configuration with up to 100 meters of cable. Or, with the addition of repeaters it is possible to expand the system up to 300 meters. The AS-i network is easy to install as there is no need for terminators at the endpoints.
Cost
AS-i networks typically reduce cabling and installation cost by around 50% compared to other conventional networks (Figure 3.2). Using a single cable to connect to discrete equipment reduces the need for cabinet, conduit, and trays. The savings generated in the use of the network can be really significant, as the use of few cables reduces installation and commissioning costs and, because it is a simple network, engineering hours.
Figure 3.2: a) Conventional systems; b) AS-i network.
Source: StoneL Corporation
The cost savings in terms of hardware and, consequently, the feasibility of the AS-i network for certain applications can be seen through the specific items shown in Figure 3.3.
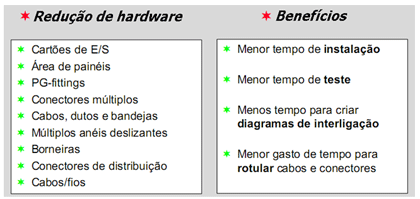
Figure 3.3: Economic viability of the AS-i system.
Source: AS-International Association (2008)
Versions and Specifications
Original Specification (1994, Version 2.04)
In the first networks, the modules (slaves) of interconnection of the final elements allowed the connection of four digital inputs and four digital outputs, resulting in a total of 124 inputs and 124 outputs in a single network (specification AS-i 2.0 or AS-i 1 ). However, in this architecture, the maximum number of slaves is limited to 31.
Its main features are related to the automatic replacement of a module in the network and the update time was easily calculated by multiplying the number of input and output modules by the deterministic network update time for each node (approximately 150 µs). This simplified calculation does not include the management phase which can be neglected for typical network installations.
Inclusion of Improvements (1998, Version 2.14)
After its release, users quickly adopted the technology and introduced new requirements regarding the version. Thus, the specification for the AS-i 2.1 (or AS-i 2) network was published.
The new features added in version 2.1 are:
  |
|
|
|
|
|
|
The chips for version 2.1 of the AS-i network are produced by two distinct consortia: Siemens and Festo jointly developed the SAP4.1 chip, pin-by-pin compatible with the SAP4 chip, and the consortium of eight other members (Bosch, Hirschmann , ifm electronic, Leuze, Lumberg, Klockner Moeller, Pepperl+Fuchs and Schneider Electric) developed the A2SI chip. Both chips provide all the functionality of version 2.1.
Additional Features (2005/2007, Version 3.0)
Until 2005, the worldwide success of the AS-i network, with approximately 10 million nodes in operation, promoted the introduction of new requirements for the network. In addition, the increasing use of Ethernet in industrial protocols demanded low-level solutions that overcome the inherent flaws of Ethernet (for example: limited topology, large data packets, high cost in the use of routers, among others). This specification helps users to define new profiles for discrete and analog data in addition to introducing a profile for serial data transmission (specification 3.0 or AS-i 3).
- Discrete input and output nodes supporting extended addressing (A/B) with 4 inputs and 4 outputs;
- Discrete input and output nodes supporting extended addressing (A/B) with 8 inputs and 8 outputs;
- Configurable analog channel (8, 12 or 16 bits);
- Discrete data channel with full-duplex serial communication.
With these new features, the AS-i network becomes an ideal partner for any other industrial protocols based on Ethernet communication. Gateways for EtherNet/IPTM, PROFINET, Modbus/TCP and others are available. Some control experts say that in the next 10 years there will be no more intermediate solutions between AS-i and Ethernet for new installations.
Characteristics
The name Actuator Sensor Interface represents its own concept. It is a simple and elegant solution for integrating discrete sensors and actuators into a process control system. This network has a series of characteristics that are presented below.
- Compatibility: sensors and actuators from different manufacturers can be connected to a standardized serial digital interface;
- Medium access control: system with a single master and cyclic scanning;
- Addressing: slaves receive a permanent address from the master or via hand-held;
- Network structure: no restrictions (linear, ring, star or tree);
- Transfer medium: two un-twisted, unshielded cables for data and power (24 VDC), typically up to 200 mA per slave, up to 8A per bus;
- Quick installation: through self-drilling connectors
- Cable size: maximum 100 m or up to 300 m using repeaters;
- Signals and power supply: they are present on the same bus (24VDC);
- Number of slaves: up to 62 slaves per network (version 2.1);
- Telegrams: telegram from the master containing the address, direct response from the slave;
- Data: 4 inputs and 4 outputs for each slave and in the case of more than 31 slaves they have only 3 outputs; (maximum 248 binary participants per network).
- Payload: Transmits 4bits/slave/message. All slaves are called sequentially by the master and receive 4 data bits. Each slave responds immediately with 4 bits of data.
- Cycle time: 10 ms for version 2.1;
- Error detection: efficient detection and retransmission of incorrect telegrams.
- AS-Interface chip: 4 configurable data I/O, 4 parameter outputs and 2 control outputs.
- Master functions: cyclic scan on all slaves, data transmission to slaves and to the control unit (PLC or PC). Network initialization, slave identification, slave diagnostics and transferred data. In addition, it reports errors to the controller and addresses replaced slaves.
- Valves: they are installed directly at the application site, reducing the piping and increasing the response speed of the actuators;
- Low cost: connection per slave and eliminates I/O modules in the PLC;
- Reliability: high level of operational reliability in harsh industrial environments;
- Open standard: developed by renowned manufacturers, affiliated to the AS-i International Association, whose transmission protocol is standardized.
- Optional: power cable for outputs and stop control.
Connectivity
The AS-i network can connect to the main control level in two ways. The first way is the direct connection (Figure 6.1 on the left). In this case, the master is part of a PLC or PC running within the cycle times determined by these devices. An AS-i master can be built by any manufacturer as it is an open standard.
The second way to connect is through a coupler (gateway) between a higher-level network and the AS-i network (Figure 6.1 on the right). Today there are couplers for other field networks, such as: Profibus, Interbus, FIP, DeviceNet, CAN, etc.
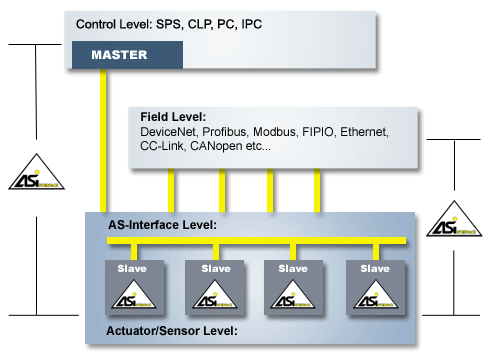
Figure 6.1 – Interconnection with other digital networks.
Source: AS-International Association (2008)
The Actuator Sensor Interface system
The name Actuator Sensor Interface represents its own concept. Although technically "AS-i" is a bus, the term interface shows that it provides a simple interface for accessing sensors and actuators in the field.
AS-i industrial networks were designed to be applied in automated environments, replacing the traditional "switch" type actuator and sensor connections with a single bus. In addition to these, it is possible to connect sensors/actuators to the bus that perform an analog/digital conversion or vice versa.
Traditionally these connections are made by pairs of wires that connect one by one the actuators and sensors to the corresponding controller, usually a Programmable Logic Controller (PLC).
The AS-i system is configured and controlled by a master, which programs the interface between a controller and the AS-i system. This master continuously exchanges information with all sensors and actuators connected to the AS-i bus in a predetermined and cyclical manner.
Figure 7.1 illustrates the AS-i system as a whole, showing its main components: cable, AS-i source with its decoupling circuit, the AS-i master and slave.
- Interface 1: between the slave and the sensors and actuators;
- Interface 2: between the equipment (source, master and slave) and the transmission medium;
- Interface 3: between the master and the host, that is, any entity that accesses the AS-i network from a higher level.
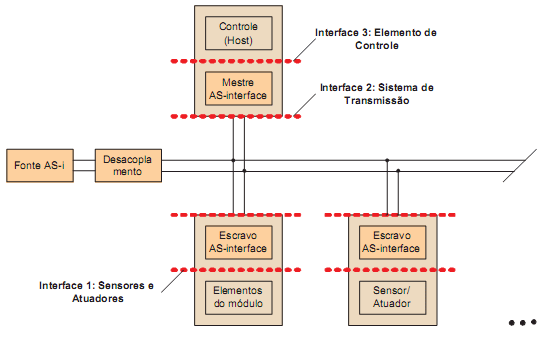
Figure 7.1: Components and interfaces.
Source: SANCHES, L.B. (2004)
7.1 Transmission Medium
The AS-Interface network connects the simplest devices in automation solutions. A single cable links actuators and sensors with the highest levels of control. AS-Interface is a standardized (EN 50295) and open network system that interconnects actuators and sensors very simply.
The connection of elements can be done in a tree, star, line or a combination of the above. There are no conventional connections and reducing the number of interconnections in terminals and connectors, not only reduces costs and assembly time, but also reduces errors.
In connection technology using parallel cables, each individual contact of a device is connected separately to the terminals and terminals of sensors and actuators. The AS-i network replaces the traditional arrangement of multiple cables, junction boxes, cable ducts, cable ducts with a single cable specially developed for the AS-i network.
The AS-i network is characterized by the fact that, in only one pair of wires, the supply of the sensors or actuators at 24Vdc and the information on their status go together. The maximum network configuration is 62 participants (slaves) that are accessed cyclically by a master at the upper control level. The reaction time is short, for all connected slaves, the response time is 10ms.
Previously, sensors and actuators had to be connected to the controller via terminals, connectors and terminal blocks. AS-i provides a reduction in installation and maintenance costs. Now, a standardized 2-wire cable enables the exchange of information and, at the same time, the power of the equipment. Slaves are connected directly to the bus without the need for additional interconnection.
This two-way flexible cable is considered the standard for the AS-i network. There is yet another circular-shaped cable that should only be used if explicitly specified by the manufacturer.
7.1.1 Standard Flexible Cable
This flexible high voltage cable complies with CENELEC or DIN VDE 0281 standards, designated H05VV-F 2X1.5 and is cheap and easy to obtain.
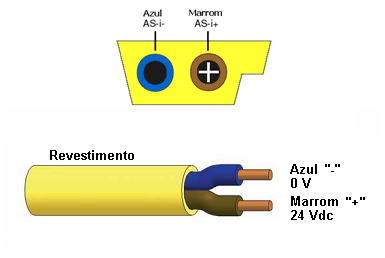
Figure 7.2: Standard AS-i bus cables
Source: AS-International Association (2008) and Turck Networks.
The AS-i, unshielded, unbraided cable has two parallel conductors and carries both data and power to the slaves. Its external insulation is yellow and has a characteristic geometric shape, designed to avoid fixing with the polarity reversed (Figure 7.3).
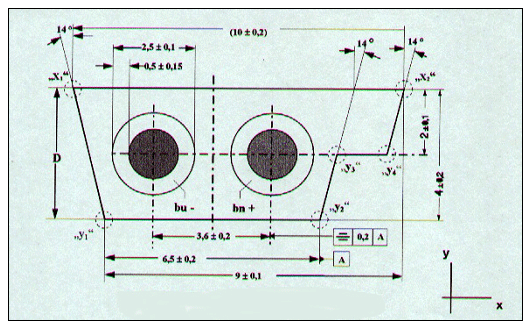
Figure 7.3: Front cut view of the AS-i cable
Source: LIAN, S.C.P. (2003).
The cable does not need to be cut or "peeled" to connect. This often causes unwanted voltage drops and is a potential source of poor contact. On the other hand, it has a very interesting form of installation, which contributes to cost savings in its implementation.
The principle is simple: the contact with the internal conductors is carried out by means of conductive sheets, which penetrate the plastic insulation to the internal copper wires.
The external coating has a "healing" property, that is, if the blades are disconnected, it closes, not showing the cut made longitudinally. It is evident that the coatings remain perforated, but do not pose a risk of short circuit due to this technique. Figures 7.4a and 7.4b illustrate the concept.
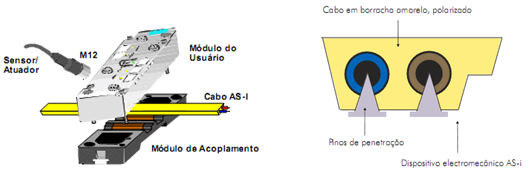
Figure 7.4: a) Coupling the module to the bus; b) Drilling pins
Source: SILVA, W.A.C.M (2008) and AS-International Association (2008).
In addition to the power available to the slaves through the yellow cable, which has become a kind of trademark of the AS-i system, and which meets almost all practical cases, supplementary power may be necessary for some slaves, especially more powerful actuators. In this case, an additional black cable is used, with the same characteristics as the first one, but exclusively dedicated to power supply. It also makes use of the penetration technique described earlier and is reserved for supplying up to 30V.
There are two relevant electrical considerations involved in selecting a suitable transmission medium: the DC resistance to the supply and the transmission characteristics in the frequency range used for communication. At least 2A of current must be able to be transmitted to supply the slaves. Within these requirements, other cables can be used, allowing designs for specific cases, such as, for example, carrying larger currents or the need for moving cables.
In addition to these two classes of cables, there is also the red version, which provides up to 230V AC.
7.1.2 Circular Cable
This cable was created specifically for the AS-i, with very similar electrical characteristics, but with a specific installation method. This cable can be shielded or unshielded, but unshielded cables with the following characteristics (at a frequency of 167 kHz) are preferably used.
- R´: < 90 mΩ/m
- C´: < 80 pF/m
- Z : 70 Ω to 140 Ω
- G´: ≤ 5 µS/m
A cable with a cross-section cut of 2 x 1.5 mm2 is recommended.
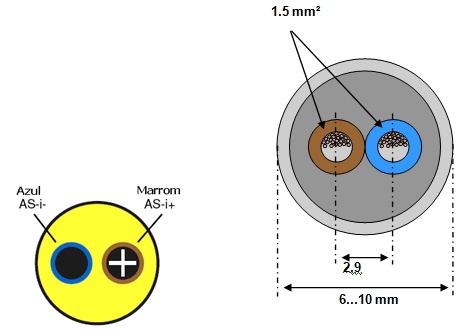
Figure 7.5: Unshielded circular cables.
Source: AS-Interface Association
7.1.3 Connections in the AS-i network
Any connections in the AS-i network other than conventional or drilling technologies must comply with the following requirements.
- Maximum contact resistance of 6 mΩ;
- Minimum allowed current of 1.5 Inom (minimum of 3A for AS-i network in general);
- Contact voltage range from 10V to 70V d.c;
- Shocks and vibrations in accordance with item 7.4 of IEC 60947-5-2;
- Breaking strength according to annex E of IEC 60947-5-2;
If clamps or terminals for screw connections are used, their thickness must be at least 2 x 2 x 1.5 mm2. If socket pins are used, type D.2 according to annex D of the standard of IEC 60947-5-2 is recommended.
7.1.4 Cable length
The maximum length of an AS-i bus cable is 100 m without the use of repeaters. If repeaters are used, a maximum length of 300 m is allowed.
The length of the AS-i bus can be calculated by adding the size of the bus cable plus 2x the size of the accessories connected to the network. Example: 50 meters of yellow cable and 5 tap-offs with 2 m of cable gives us a net the size of: 50 + 2 x 5 x = 70 m.
In Figures 7.6 and 7.7, solutions for extender and repeater connections are presented in order to increase the length of the AS-i bus.
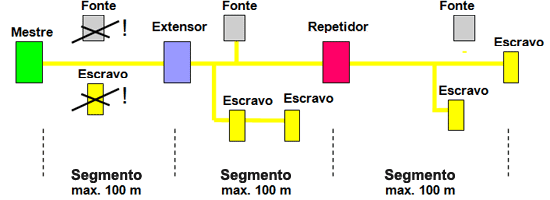
Figure 7.6: Solution with an extender and a repeater
Source: AS-Interface Association.
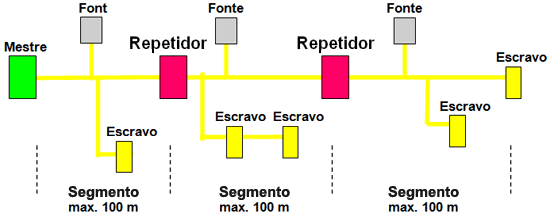
Figure 7.7: Solution with two repeaters
Source: AS-International Association (2008).
7.2 Power Supply
The AS-i source has four functions in the system as described below.
7.2.1 Power Supply
The power supply unit works at a voltage of 29.5V to 31.6V DC and under normal operating conditions, provides a current of 0A to 8A. The power supply supplies power to the slaves and partially to the master through two wires, the same used for AS-i data transmission, and can be connected to the network at any point. On long lines, the voltage drop must be considered and should generally not be greater than 3V. The power supply has internally an overload protection circuit with current limit
7.2.2 Balancing
The source is also responsible for balancing the AS-i network. AS-i is operated as a symmetrical, ungrounded system. For noise immunity the AS-i cable needs to be installed as symmetrical as possible. This is possible through the balancing circuit shown in Figure 7.8. The shield connection must be connected to an appropriate point on the machine or system. Only that point can be connected to system ground (GND).
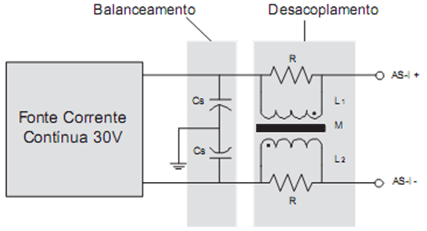
Figure 7.8: Simplified Schematic Diagram of the AS-i source
Source: SANCHES, L.B. (2004)
7.2.3 Data Decoupling
The third function of the source is to provide data decoupling. The decoupling network, which is usually found in the same module as the power supply, consists of two inductors of 50µH each (L1 and L2) and two resistors in parallel of 39Ω each. The inductors perform a differentiating operation on the voltage pulses to convert the current pulses generated by transmitters connected to the network. At the same time, they prevent a short circuit in the cable. The coupling between the inductors must be as close as possible to 1, which is to say that the mutual inductance must tend to 200µH.
7.2.4 Security
The fourth function is a security consideration. The AS-i system was designed as a system for low voltages with safe isolation (Protective Extra Low Voltage). This means that according to the relevant IEC standards, "safe isolation" is required from the source between the supply network and the AS-i network.
7.3 Redundancy
This issue is not very common in AS-i networks, because it is a network in which discrete communication predominates and also because of its robustness, determinism and simplicity. Redundancy can be done at the master and power supply levels. There is still no redundancy in terms of cables and slaves.
It is possible in a network to have a redundant master. This master remains in monitoring mode and when it perceives a failure or lack of communication from the active master, it will take control of the network. Regarding the power supply, this is also possible using a “Power Extender”, in this way the two supplies are connected in redundant mode.
7.4 Sensors and Actuators (Interface 1)
7.4.1 The AS-i Slave
The AS-i slave, as seen in Figure 7.1, makes the connection between the transmission system and interface 1, in which the sensors and actuators are connected. The slave feeds them and manages their communication with the master. From the beginning of the development of the AS-i specification it was clear that the slave had to be small and compact in order to be able to be integrated directly with the sensors and actuators. This was achieved thanks to the use of integrated circuits, giving rise to the famous AS-i chip.
The AS-i slave chip allows sensors, actuators and/or modules to be connected to the AS-i bus as a slave device, recognizing output commands from the master and sending response data. A large number of sensors and actuators used lately in automation allow a low cost per connection in AS-i slave devices. In the case of analog devices, the data exceeds 4 bits of useful information per cycle. In this case, the data is split and sent in several cycles. There are two possibilities for using an AS-i slave chip:
The AS-i chip can be embedded in sensors or actuators (Figure 7.9), in this way the elements are integrated with AS-i and all data bits and parameters are available to the device (sensor or actuator).
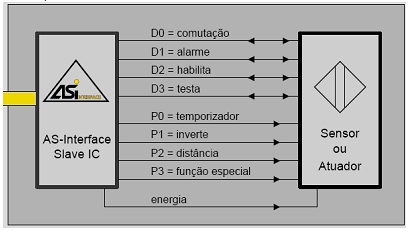
Figura7.9: Sensor ou atuador com AS-i embutido.
Fonte: AS-International Association (2008).
Another way is to use an AS-i slave chip built into modules to which conventional sensors and actuators can be connected. Figure 7.10 shows a module with two inputs for sensors and two outputs for binary actuators.
Regardless of how the slave is implemented, it will have the architecture shown in Figure 7.11, in which connections to interface 1 can be physical or logical and connections to interface 2 are necessarily physical.
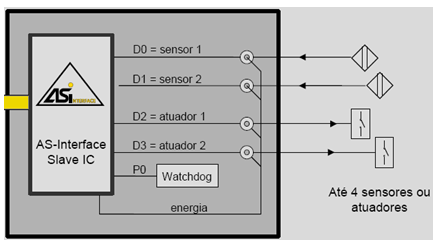
Figure 7.10: 2E/2S module for conventional sensors/actuators.
Source: AS-Interface Association.
In the power block, the data signals are separated from the power component by means of an inductance. To implement it in an IC, this inductance is performed electronically, and ensures that the slave maintains a sufficiently high resistance in the frequency band of the communication data. The supply voltage is supplied at the Vout terminal.
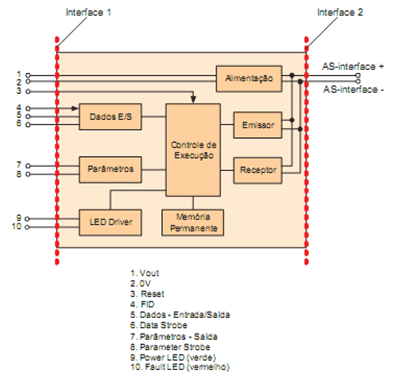
Figure 7.11: Architecture of an AS-i slave
Source: SANCHES, L.B. (2004).
The receiver the voltage pulses detected in the AS-i cable are filtered, digitized and recorded. At this time, the received signal is submitted to error detection tests, to ensure that noise has not corrupted the master's request.
At the sender, the information from the send register is encoded and sent over the bus as a sequence of current pulses according to APM modulation.
Finally, the execution control decodes the master's requests, checks if it has errors, performs the command encoded by it and, if so, produces a response to be sent. The execution (or sequence) control also has a non-volatile memory area.
The slave registers and flags are as follows:
- Address Register: This 5-bit register contains the current address of the slave. If the address of a request from the master is the same as the address contained in it, the slave will then respond to the request. After a reset, the register is filled with the address value contained in the slave's non-volatile memory. Its content can be changed by the master through the delete address and address assignment requests.
- Identification Registers: These registers contain the I/O configuration and the ID code of the slave. With the exception of the ID Code 1 register, which can be changed by the master, the others are permanent and recorded during their manufacture.
- Output data register: The Data Output register is four bits and contains the data of the last data request from the master (data request) that was received without errors by the slave. The bits that are related to an output according to the I/O configuration represent the value of that output, while the others are ignored. After a reset, the register is loaded with the default hexadecimal value F.
- Parameter Register: This 4-bit register contains the last value of parameters received from a valid parameter request. The bits correspond to the output ports of the parameters.
- Receive register: This register contains the last request from the master for processing in execution control.
- Send register: This 5-bit register contains the slave response to be sent.
- Status Register: The status register contains 3 bits to indicate certain slave status conditions:
- Flag S0: it is high during the slave address recording process.
- Flag S1: is high if the FID input reports a peripheral error.
- Flag S3: is high if an error occurs while reading the slave address in non-volatile memory
- Synchronization Flag: If the slave correctly received a request from the master, decoded it and sent a response, the synchronization flag is activated. In the synchronized state, the master pause is monitored after a request for only one bit time, and the slave response starts after two bit times.
- Data exchange blocked flag: This flag is activated by a reset and deactivated by the error-free reception of a request for parameters. This mechanism prevents data requests from being accepted without the parameter ports having been loaded with the nominal parameters. This behavior is necessary to avoid inconsistencies between the slave and the master. It can happen, for example, that a slave is restarted (reset) due to a brief power failure, without the master being aware. This would cause the parameters to be reset, while the image the master keeps of them remains the same. The slave may then respond differently than expected by the master, causing unwanted problems. For this reason, a data exchange can only be carried out after a parameter request by the master.
7.4.2 The Interface 1
As indicated in Figure 7.11, interface 1 of the slave has 4 data ports that, depending on the I/O configuration, can be used as inputs, with outputs or as bidirectional ports. An output data strobe is also provided, which signals when output data is present and when input data is expected.
For actuator slaves, it is recommended that the timeout monitor, known as a watchdog, which is integrated in the slave circuit, be activated. If within a specified time a new correct data request ("data request") is not received at the slave address, the actuator can use the watchdog signal to go to a safe state.
This mechanism allows a range of error possibilities to be covered, such as master hardware failure, transmission cable interference, or slave address loss. When necessary, an AS-i system can then be more secure. Normally, a value between 40 and 100ms is specified as the timeout period.
In addition to the data ports, which allow cyclical data exchange with the master, ports for acyclical exchange of parameters between the master and the slave are present. There is also, again, a parameter strobe output to indicate the receipt of a new parameter message.
The "FID" input is used to signal peripheral faults. If the slave electronics detects an error, this input can be used to signal such an event locally, through LEDs and report it to the master through status bits. The master can then insert the slave into a slave list with peripheral errors, and report it in turn to the higher control levels.
Finally, a direct current output, which is generally in the 24V +10/-15% range, provides power to the sensors/actuators.
7.5 Transmission Systems (Interface 2)
Interface 2 includes the specifications necessary for the effective exchange of data between the elements connected on the AS-i bus. It defines the form of access to the physical medium, the exchange of data at the electrical level and the handling of some communication errors, as well as the time requirements in the transactions.
7.5.1 Network Structures
The network topology of the AS-i system is left to the user, which simplifies its design. The restriction that must be observed is the maximum cable length limit of 100m. It is also important to note that no terminal impedances are required, which also simplifies installation. Tree, linear, star and even ring structures are allowed (Figure 7.12). In case of need for longer connections, repeaters can be used, expanding the network reach, as long as the limits of 62 slaves and one master are respected.
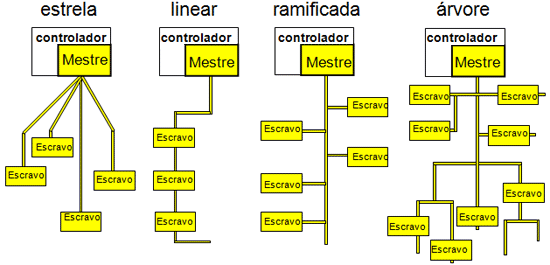
Figure 7.12: Physical network topology.
Source: AS-International Association (2008)
7.5.2 Modulation
The selection of a suitable modulation for AS-i had to meet a set of very demanding requirements, which led to the creation of a new modulation procedure, known as Alternating Pulse Modulation (APM). These requirements include:
- The message signal superimposed on the supply voltage must be free of direct current component.
- The slave's transmitter, and when possible, the master's, should be able to be implemented in a simple way, which takes up little space and low cost.
- Since AS-i cable has an impedance that increases greatly with frequency, the data signal must have a relatively narrow band.
- High levels of noise radiation are also unacceptable.
APM modulation is a procedure for baseband serial transmission and can be seen in Figure 7.13. The bit sequence is initially encoded so that a phase shift occurs whenever the signal changes (Manchester encoding). The result is a send current that in conjunction with a single inductor in the system uses differentiation to generate the desired voltage signal across the conductors.
Each rise in the send current results in a negative voltage pulse, and each drop results in a positive pulse. In this way, it is quite simple to generate signals in the slaves with a voltage higher than their supply voltage. This means that inductors can be eliminated in the slaves, which keeps the integrated electronics small and cheap. On the receiver side, these voltage signals are detected on the line and converted back into the sent bit sequence. The receiver synchronizes itself with the detection of the first negative pulse, which is interpreted as a start bit. If the voltage pulses approach sen2 type pulses, then the requirements for low threshold frequency and low noise emission are met at the same time. This is achieved by properly shaping the sent current pulses which is generated as the integral of a sin2 pulse. Using this modulation and allowable topologies 6µs bit times are obtained. This allows a baud rate of around 167kBit/s.
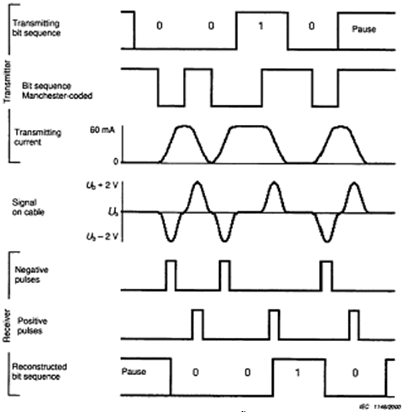
Figure 7.13: APM modulation.
Source: SANCHES, L.B. (2004).
As the cables do not have terminators, the message pulses have a large amplitude variation. By being able to deal with this problem, caused mainly by reflections at the end of the cable, which reach higher frequencies, the AS-i presents itself as an extremely robust system.
7.5.3 Access to the Medium
As AS-i was designed to replace star-type point-to-point connections, a media access procedure that reproduces this topology and guarantees a defined response time was selected - master-slave access with cyclic polling. The master sends a telegram that is received by the slave at a particular address and the slave contacted at that address responds within the allotted time. This operation is referred to as a transaction. The transmission system allows the connection to the bus of a master and up to 62 slaves.
The chosen procedure allows the construction of very simple and therefore cost-effective slaves, while providing flexibility and integrity. In the case of small disturbances in the network, the master can, for example, repeat telegrams to the address from which it received no response, or an invalid response. AS-i messages, therefore, are of two types: those sent by the master and those sent by the slave. Figure 7.14 illustrates a transaction and the times involved. It consists of:
- a request from the master,
- a master's break,
- a response from the slave and
- a break from the slave.
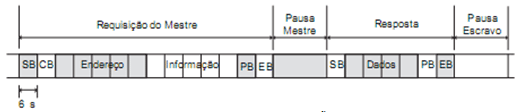
Figure 7.14: An AS-i transaction.
Source: SANCHES, L.B. (2004).
A requisição do mestre se estende sempre por 14 tempos de bit, e a resposta do escravo por 7. Um tempo de bit corresponde a um intervalo de tempo uniforme de 6µs. A pausa do mestre deve estar em um intervalo de no mínimo 2 tempos de bit e um máximo de 10 tempos de bit. Se o escravo está sincronizado, ele pode começar a transmitir tão logo 2 tempos de bit tenham se passado, caso contrário ele necessitará mais dois tempos, haja vista ele estar monitorando a pausa do mestre neste período para qualquer informação adicional antes de aceitar a chamada como válida. O mestre, no entanto, caso não tenha recebido resposta dentro de no máximo 10 tempos de bit, pode assumir que não haverá resposta e iniciar a transação seguinte. A pausa entre o final de uma resposta do escravo e a próxima requisição do mestre deve estar entre 1,5 e 2 tempos de bit.
The master request always extends by 14 bit times, and the slave response by 7. A bit time corresponds to a uniform time interval of 6µs. The master pause must be within a range of a minimum of 2 bit times and a maximum of 10 bit times. If the slave is synchronized, it can start transmitting as soon as 2 bit times have passed, otherwise it will need two more times as it is monitoring the master's pause in this period for any additional information before accepting the call as valid. The master, however, if it has not received a response within a maximum of 10 bit times, it can assume that there will be no response and start the next transaction. The pause between the end of a response from the slave and the next request from the master must be between 1.5 and 2 bit times.
A master request consists of:
- Start Bit (SB). Identifies the start of a master request on the bus. Its value is always "0".
- Control Bit (CB). Identifies the type of request: "0" for requesting data, parameters or address assignment and "1" for command calls.
- Address(A4..A0). Slave address requested.
- Information (I4..I0). These 5 bits make up, depending on the request to be made, the data passed to the slave.
- Parity Bit (PB). The number of bits with value "1" in a request, except for the end bit, must be even.
- End Bit (EB). Identifies the end of a master request. It always has value "1".
And a response from any slave consists of:
- Start Bit (SB). Identifies the start of a response from the slave. It always has the value "0".
- Information (I3..I0). These bits make up the information properly passed to the master.
- Parity Bit (PB). Like a request, a response must also have even parity.
- End Bit(EB). Always set to "1", it signals the end of a response from the slave.
Version 2.1 of the AS-i specification (1998) created the possibility to address twice as many slaves as previously allowed. With it, up to 62 slaves can be connected. For this to be possible, a bit of the information field is used as what is conventionally called "select bit", or, selection bit. Thus, the slaves connected to the bus were divided into two groups of 31 slaves at most each: group A and group B. Thus, a slave started to have, in addition to an address, a type - A or B. This modification was introduced in so as not to lose the compatibility of slaves of the old version with masters of the new version.
Previous version slaves can be addressed normally, but they occupy two addresses each. For them there is no distinction between slave "A" or "B", and they do not recognize the selection bit as such, but as a normal bit of information. Masters conforming to the new version have the means to identify the type of a slave and send the requests properly. This will be seen later.
7.5.4 Error Handling
Reliable error recognition is of great importance for flawless communication over AS-i cable, which is usually unshielded. Due to the fact that the AS-i telegrams involved in the transactions are quite short, error detection is different from that applied in general to other field networks. The master request has only 11 data bits to check, and the slave response has 4 bits. Adding error-checking bits to messages would cause the baud rate to drop dramatically. Instead, AS-i makes use of known message sizes, specified bit patterns, and alternating pulse modulation to be able to distinguish the following errors:
- Start Bit Error;
- Toggle error;
- Pause error;
- Information Error;
- parity error;
- End Bit Error and;
- Telegram size error.
Each request from the master and each response from the slave is subjected to a check of these 7 types of errors. If any of them are detected, the request (or response) is considered invalid.
7.5.5 Analog I/O Signals
AS-i supports analog signal transmission. For this, the digitized analog value will be separated into several parts and transmitted, through several cycles. For an analog input signal of 12 data bits, 6 cycles will be required, constituting a total transmission time of 30 ms (in version 2.1 of the AS-i specification). An A/D conversion circuit must be an integral part of the slave device that has analog I/O.
This circuit will not only convert signals, but it must be able to freeze the converted value until all bits are fully transmitted, and only then will it be ready to resample the analog signal.
AS-International has defined a standard for transmitting analog signal values (defined in profile S-17 of the AS-Inteface specification). To facilitate practical use, some PLCs already offer function blocks for application with analog signal values.
To ensure data consistency between master and slave, a handshake bit was set in this profile, which is inverted by the slave and then returned. So, the master can check if it already has a response from the slave and the slave can check if the master wants to repeat the last request or if it wants the next piece of data. On the other hand, this reduces the payload in each frame to 3 bits per cycle. However, it ensures correct data transmission even with disturbances. For analog inputs, the master requests and the slave responds; for analog outputs the slave requests and the master responds.
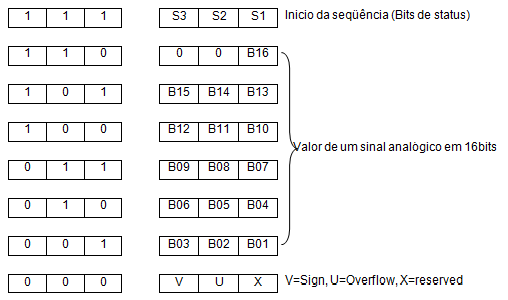
Figure 7.15: Transmission sequence of an analog value.
Source: ATAIDE, F.H. (2004).
7.6 The AS-i Master (Interface 3)
The AS-i master makes the connection between a controller or a Fieldbus system (Host) and the sensors and actuators of the AS-i network. It manages the message traffic on the bus independently, so that for the Host the sensors and actuators are seen as in the traditional architecture. In addition, the master provides additional configuration and diagnostics functions for the AS-i network.
The AS-i specification divides the master into three layers, which describe it from the transmission cable to interface 3 (Figure 7.16).
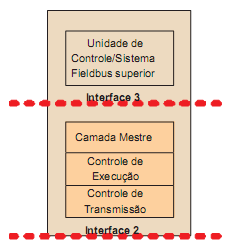
Figure 7.16: Layered structure of the AS-i master
Source: SANCHES, L.B. (2004)
The physical transmission of master requests is specified by interface 1 and has basically the same characteristics as the slave.
The lowest logical layer is the transmission layer, which is responsible for transmitting and receiving individual telegrams. Automatic repetition of telegrams when a slave response fails is possible, ensuring integrity for the upper layers.
Sequence control, or execution control, is just above the transmission layer and passes data transmission requests to it. The function of this layer is to control the sequence in which the telegrams are sent, and also to process the functions called by the upper layer, generating the telegrams correctly and in the required sequence.
The highest layer is called the master layer, and it interfaces with the host.
7.6.1 Master's Requests
The AS-i master performs its function of interconnecting interfaces 2 and 3 through messages sent to the slaves, one by one. We will present here the possible requests - which are few - that the master can make to a particular slave, through interface 2, as well as the expected behavior of the slave in the face of these requests, that is, its responses.
Figure 7.17 presents all possible requests that a master can make to a slave, based on AS-i specification 2.1, which supports extended addressing. It can be observed in the requests the presence of a select bit. This bit takes the place of a bit previously used for common data exchange. With the addition of this new bit, it became possible to address twice as many slaves initially as possible: 62. The slaves then started to have, in addition to an address between 0 and 31, a type: A or B, which is defined by the bit of selection (select bit ).
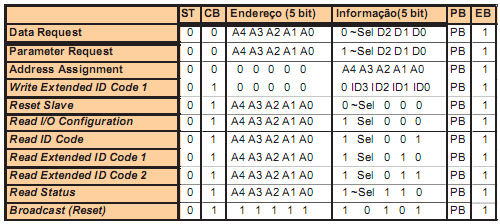
Figure 7.17: Requests from a master from the 2.1 specification
Source: BECKER et al. (2002)
These requests are analyzed one by one below.
Read IO configuration: Through this request, the master receives the input and output configuration (IO configuration) from a slave as a response. Together with the slave ID code, the IO configuration uniquely identifies a type of slave. The IO configuration refers to the behavior of the slave interface 1 data ports, and is defined as shown in Figure 7.18.
In this definition, IN means a process input, OUT an output, I/O a bidirectional behavior of the gate, and TRI indicates a high impedance output with no function. The latter case is accepted when, during a reset, a slave memory reading error does not allow an unambiguous identification to be defined.
Whenever an output is set (OUT), it means that the corresponding information bit in the slave's response is undefined. Likewise, an information bit of a master request referring to an input (IN) port is undefined, even when the bit is high.
The I/O configuration allows unnecessary information to be hidden. Together with the ID code they constitute a slave profile. It is defined by the manufacturer, is always 4 bits long, and cannot be modified by the user.
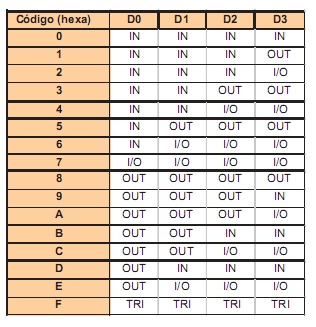
Figure 7.18: Input and output configuration codes
Source: BECKER et al. (2002)
Read ID Code: The ID code of slaves that comply with version 2.1 of the specification have, in addition to the original ID code, read by the master through the "Read ID Code" request, two other codes - "Extended ID Code 1" and "Extended ID Code 2". Together they serve to identify different slaves. Slaves conforming to the new specification, for example, have an ID code "A", in hexadecimal, while an ID code "B" indicates a "safety at work" slave. All slaves with ID code equal to "A" also have the other two ID codes.
Read Extended ID Code 1: This call, similar to the previous one, is used to read extended code 1 from the slave, when it exists. This code, unlike the original, can be modified by the user.
Read Extended ID Code 2: This code extends the configuration possibilities of the slaves, and just like the original ID code, it cannot be modified by the user, being definitively defined by the manufacturer.
The profile of a slave, constituted by the set of ID codes and the I/O configuration, contains the definition of the behavior of the parameters, data ports and other additional characteristics of the slave.
Data Request: This call is the most frequently used in AS-i, and it is the one that allows assigning values to the slave's data outputs on interface 1, and obtaining the input value as a response. As stated before, the behavior of the ports is defined by the I/O configuration. Data ports can be used in different ways, not just as binary inputs and outputs of process variables. They can also be used for additional configurations, and also as a digitized representation of analog process variables.
Parameter Request: This call is used by the master to send a bit pattern to the parameter output ports on interface 1 of a slave, which can control certain behaviors on the slave. The last value sent is kept in the slave until a newer one is received or a reset occurs. For a standard slave there are 4 parameter bits in the call, while for slaves with extended addressing only 3, as one of them is used as a select bit. This call cannot be made to a slave with address 0, as it will be interpreted differently.
Address Assignment: This command allows assigning a new address permanently to a slave with address 0. The slave sends an acknowledgment response and at the same time starts the non-volatile memory recording process, which cannot last longer than 500ms. During the process, the slave starts to respond to requests at the new address. This request is the one that allows replacing damaged slaves without needing to restart the network.
Reset Slave: This call triggers the process that puts the slave in its initial state, and has the same effect as a power-up reset or the one triggered by the corresponding port of interface 1 of the slave. It cannot last longer than 2 ms.
Delete Operating Address: The command "Delete Address" is used to temporarily delete the address of a slave and is used in conjunction with "Address Assignment", because it can only be used with a slave with address 0.
For example, to change the address of a slave, first the request "Delete Address" is used, then "Address Assignment". The slave recognizes the receipt of a "Delete Address" request without errors, responding with 0 (in hexadecimal), and starts to respond at this address. To restore the old address, a reset needs to take place on the slave.
Read Status: This request is used to get the value of the status register of the accessed slave. Its content is returned in the slave's response. The register contains three flags with the following meaning:
- S0: "Address Volatile". This flag is activated when the internal routine of the slave that permanently writes a new address is in progress.
- S1: "Peripheral Error". This flag is activated when the slave detects a high input on the FID port of interface 1, indicating an external fault in the equipment.
- S3: "Read error non-volatile". This bit is activated when there is an error reading the slave's non-volatile memory after a reset;
Bit S2 is not yet used and is reserved for future use. The master can use the slaves' status information to perform diagnostic functions. Slaves conforming to the 2.0 specification do not support the "Peripheral Error" flag.
Broadcast requests of this type are received by all slaves and are characterized by not requiring a response from the slave. In this sense, they are abnormal in AS-i and so far only one reset request is defined as broadcast.
7.6.2 The Transmission Layer
The transmission layer, also known as transmission control, is responsible for exchanging individual telegrams with the slaves. It receives from the execution control a sending request, together with the data that will be sent through the communication channel, adding to them the start bit, the parity bit and the end bit, thus generating the frame (telegram) of the teacher. This telegram is sent following the time requirements of the transmission system as described in section 7.5.
It is possible that the execution control request is of two types: single transmission or not. In the first way, in case there is no response from the slave after the waiting timeout or the response is not valid, the transmission control immediately reports the error to the upper layer, without resending the telegram. In the second form, the error is only reported after a second unsuccessful attempt. On the other hand, if the transaction is successful, the transmission control provides the execution control with the data sent by the slave, without the additional start, end and parity bits. It is also up to the transmission control to report an AS-i Power Fail (APF) signal, which indicates voltage below the lower limit on the AS-i bus.
Figure 7.20 illustrates the state machine that models transmission control behavior. MT stands for multiple transmissions and means that transmission control repeats sending a telegram in case of error the first time.
Alternatively, ST is equivalent to single transmission, in which case the error is reported after the first failure. State transitions occur as a function of logical operations represented by the operators in italics and and or. Inputs and outputs are separated by a slash ("/").
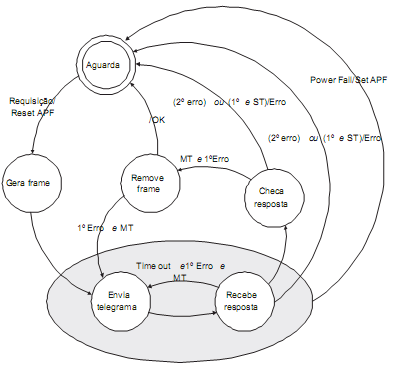
Figure 7.19: Transmission Control
Source: SANCHES, L.B. (2004)
The execution control, or sequence control, is responsible for generating the AS-i telegrams in the correct sequence, using the service of sending individual frames provided by the lower layer. For this, it has a set of data fields and lists that allows to keep an image of the AS-i network and its slaves constantly updated, which in turn is used by the upper layer to implement the interface with the host.
These data fields are shown below:
Input Data Image (IDI): This field contains the most recent copies of the data received from the slaves through the so-called "Data Request". Each slave occupies 4 bits of memory.
Output Data Image (ODI): This field contains the most recent data written by the host to be sent to the slaves by a "Data Request" call. Here, too, four bits are needed for each of the 62 slaves.
Analog Input Data Image (AIDI): This field contains the data received from the analog inputs of slaves according to profiles 7.3 and 7.4, similarly to the IDI data.
Analog Output Data Image (AODI): This field, similar to the previous one, contains the most recent values to be sent to the analog outputs.
Configuration Data Image (CDI): This field contains the I/O codes and ID codes of each slave. Therefore, 2 bytes are required for each slave.
Permanent Configuration Data (PCD): This field is similar to the previous one, however it is in a non-volatile area. The ID codes or the I/O configuration of a slave not present on the network are filled with the value F(hexadecimal).
Parameter Image (PI): This area is reserved for the 4 parameter bits of each slave. Therefore, every two slaves occupy one byte.
Permanent Parameter: This field has the parameters configured for each slave, and is in a non-volatile area, just like PCD.
List of Detected Slaves (LDS): Each slave corresponds to a bit of this list, which is activated when the slave has been detected correctly.
List of Activated Slaves (LAS): In this list the bit corresponding to the slave is activated when it has been activated correctly.
List of Projected Slaves (LPS): This list is in non-volatile memory and represents the slaves that are expected to be connected to the AS-i network when it is turned on.
List of Peripheral Fault (LPF): In this list the bit corresponding to the slave is activated when a high signal is detected on the FID pin (section 7.4) of the slave.
In addition to these data fields, the execution control reports master states to the host via some flags. These flags are as follows:
- Config_OK: This flag is activated when the nominal and real detected configuration are in agreement. This is a simple way to get information about the configuration;
- LDS.0: Indicates the presence of a slave with address "0" - which is not allowed in normal operation;
- Auto_Address_Enable: Indicates that automatic addressing is enabled;
- Auto_Address_Available: Indicates that conditions exist for automatic addressing to occur *
- Mode: Indicates whether the master is in "Configuration" (1) or "Protected" (0) mode;
- Normal_Operation: Indicates that the master is cyclically transitioning between normal operation phases;
- APF: "AS-i Power Fail" - indicates bus voltage below the lower limit;
- Offline_Ready: Activated when the offline phase is complete;
- Periphery_OK: Indicates that the List of Periphery Fault is empty;
- Offline: When activated by the user, takes the master to the offline phase;
- Data_Exchange_Active: Enables data exchange between master and slave.
* As a matter of terminology, confusion may occur between this flag and the previous one. Note that the first is user-defined, allowing auto-addressing if conditions are met, which is indicated by the Auto_Address_Available flag
It is important to note that four of these flags are enabled by the user - host - and affect the behavior of the master: the last two in the list, the "Auto_Address_Available" flag and the "Mode" flag. All others cannot be changed by the user and are controlled by the master himself.
The behavior of the master is divided into several steps, or phases, that are performed by the execution control.
Figure 7.19 illustrates the state machine that models execution control behavior. The dashed area indicates the normal operating mode, that is, when the master performs cyclic data exchange with the configured slaves, keeping the "Input Data Image" area and the data ports updated according to the "Output Data Image" area. . In addition to the exchange of input and output data, carried out in the "Data Exchange" phase, network management information is exchanged in the other two phases during the normal operating cycle.
The detailing of the operations in each one of the phases will allow to apprehend all the behavior of the execution control, and consequently of most of the master.
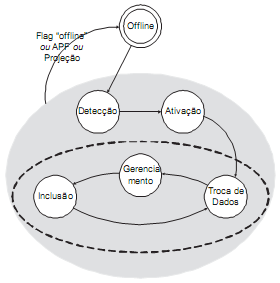
Figure 7.20: Phases (states) of execution control
Source: SANCHES, L.B. (2004)
7.6.4 Transmission Phases
After the power supply is turned on, the master transitions between the different phases (states). The master's initialization takes place in the offline phase, followed by the detection phase, in which the slaves connected to the bus are detected. Once detected, the slaves are activated in the next phase, being ready to enter the normal operation cycle (outlined in Figure 7.20), composed of a data exchange phase, a management phase and, finally, an inclusion phase. Just as the cycle between the data exchange, management, and inclusion phases is distinguished by normal operation, the offline phase makes up the master's start-up, while the detection and activation phases make up the master's start-up.
Startup
The offline phase puts the master in a position to start operations. During it, the "Input Data Image" field is filled with zeros (inactive inputs), and the "Output Data Image" field is filled with "ones" (inactive outputs), which guarantees a known initial state for all ports. slave data.
The master can be brought to the offline phase of any other phase, by activating the offline flag, which therefore has the function of restarting the entire network.
Start-up
In the start-up operation, the slaves are first detected and then activated. In the detection phase, the master sends requests to read the IO and ID codes of the slaves, one by one. Slaves that correctly respond to calls are considered detected, and become part of the Detected Slave List (LDS). Their respective IO and ID codes are stored in the Configuration Data Image (CDI) field. In the activation phase, the Master's operating mode is taken into account, which can be:
1. Configuration or;
2. Protected (also called projection).
In configuration mode, all LDS slaves are activated, by sending a "Parameter Request", in which the slave's parameter outputs are written, and a "Data Request", which writes to the corresponding ports of the slaves. If the slave correctly responds to these two calls, it is then activated, and becomes part of the LAS. In projection mode, only the slaves present in the LDS, which are also in the "List of Projected Slaves" and which have the same IO configuration and the same ID codes corresponding to the non-volatile fields are activated. The master then exchanges data only with the pre-configured slaves. At the end of the activation phase, a check is carried out, and if the nominal (detected) and projected configuration agree, the Config_OK flag is activated. Figures 7.21 and 7.22 present the flowcharts that represent the behavior of the master in the detection and activation phases.
Normal Operation
The process input and output data exchange takes place in the Data Exchange Phase or ("Data Exchange Phase"). The so-called normal operation also includes the management phases ("Management Phase") and Inclusion ("Inclusion Phase").
Under conditions in which the sensors and actuators are operating normally in the plant, connected to the AS-i bus, the master cyclically transitions between the three phases that make up the so-called normal operating condition. In each cycle, the management phase is entitled to an AS-i transaction, as is the Inclusion phase. This mechanism allows maintaining a high scanning speed of all slaves, updating their output data and reading the input data in the same transaction, without harming the network management operations that occur in the other two phases, and which can be completed. in several cycles. Figure 7.22 illustrates the behavior of the master during the Data Exchange phase. It can be seen that communication with a particular slave needs to fail through 3 cycles for it to be removed from the lists of detected (LDS) and activated (LAS) slaves.
This guarantees a proper functioning of the network even in situations that are more subject to noise causing failures. In the latter case, the Config_OK flag is deactivated.
After the Data Exchange phase is complete, the master enters the management phase. In this phase, acyclic telegrams are sent to the slaves. Unlike the Data Exchange phase, in which all activated slaves are accessed before the next phase, here only one telegram is sent, and therefore functions that require more than one telegram to be completed are executed through several cycles.
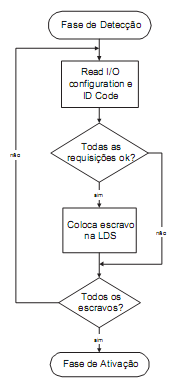
Figure 7.21: Flowchart of the detection phase
Source: SANCHES, L.B. (2004)
In the management phase, the master makes use of the various possible requests to perform tasks requested by the host. In case there are no functions to be performed, the master can send status reading telegrams, "dumb" telegrams or even not send telegrams at this stage.
After the management phase, the Inclusion phase takes place, in which new slaves are sought at the end of each cycle. During each cycle a slave is requested. This call is performed by transmission control without retry on error, because an error here is not critical. If a slave that is already activated responds, or if there is no response, the next slave is requested in the next activation phase. If a slave that has not been activated so far responds, its ID codes are requested in the next phases, and the LDS is then updated.
In the next phase, depending on the master's operating mode, the slave is activated, entering the LAS. Activation is performed by sending a request for parameters to the slave, which are updated according to the PI field ("Parameter Image"). Finally, in the last step, the master makes a data request, sending input data according to the "Input Data Image".
It can be seen, therefore, that the inclusion of a slave occurs in the same way as the start-up procedures. If a slave with address 0 is detected during the inclusion phase, even if a designed slave is not absent, automatic addressing is blocked by deactivating the "Auto_Address_Available" flag. The same occurs when a slave found is not designed. The Config_OK flag is activated at the end of each inclusion phase. Soon after a new cycle begins with the Data Exchange phase.
It is important to note that each phase of the normal operating cycle alternates between a group of type A and type B slaves. Prior to the emergence of extended addressing, this did not happen, as there were not both types of slaves. After version 2.1, however, the cycle occurs alternately, as Figure 7.23 illustrates. It should also be noted that slaves conforming to the old specification are accessed in all cycles, as they do not have the A/B differentiation. In this way, the data scan cycle in the extended addressing is double that of the previous one, but slaves of the old specification continue to exchange data at the previous cycle time.
7.6.4 The Master Layer and Interface 3
The interface between the master and the host (interface 3) is only defined logically, leaving the implementation to the manufacturer. It is specified by the standards only in the form of functions that the master must fulfill. The master layer is the one that adapts these functions to the specific host. It has already been said that the host is usually another higher-ranking fieldbus system, a PLC or a PC. Therefore, the ways to access the master, and therefore, to an AS-i network, occur in the most varied ways. In case the host is a PC, for example, the master can be on a board connected to the motherboard and accessed through drives that implement the functions defined by interface 3 and adapted for that system in the master layer. The possibilities are virtually endless.
In the case of a PLC, the master is almost always an external module, seen as a common I/O module, and which is accessed through properly mapped memory areas. The interface implementation, therefore, is different from the previous case. The same reasoning extends to the case of AS-i gateways. There are AS-i gateways for Profibus DP, for DeviceNet, for Modbus and others on the market.
There are few functions that lead the lower layers to an effective exchange of data between the master and the slave. Most of them access the master's data fields, which maintain an up-to-date picture of the network in order to obtain the information they need. Those that lead to data exchange are carried out in the management phase, which has the right to send a telegram every cycle.
The functions:
- "Read Input Data" e
- "Write Output Data"
access the "Input Data Image" and "Output Data Image" fields to return or write the data properly.
- "Write Parameter"
escreve um conjunto de parâmetros na "Parameter Image" e também faz com que uma requisição de escrita de parâmetros ocorra na fase de gerenciamento. Dessa forma, quando uma chamada.
- "Read Parameter"
is performed by the host, it is not necessary to access the slave directly, but only the image of the parameters, which is always updated with the real parameters in the slaves.
In addition to these there are:
- "Get LDS",
- "Get LAS" e
- "Get LPS".
that return the corresponding lists, also accessing the appropriate data fields from the execution control.
Permanent data is accessed by
- "Get LPS";
- "Get Permanent Parameter";
- "Get Permanent Configuration";
and recorded by the correspondents
- "Set LPS",
- "Set Permanent Parameter" e
- "Set Permanent Configuration".
It is important to point out that the functions that write data permanently take the master to the offline phase, restarting its behavior.
It is also possible to read the configuration fields, through the functions
- "Read Actual Configuration Data" e
- "Read Parameter Image".
The functions
- "Project Actual Configuration Data" e
- "Project Actual Parameters"
allow you to implement one of the features of AS-i that most contribute to its simplicity of use: the fact that a configuration detected as permanent can be stored, so that the configuration of the AS-i network becomes quite simple.
Finally, it is possible to obtain information about the behavior of the master through:
- "Get Flags"
and configure it by
- "Set Configuration Mode",
- "Set Offline Mode" e
- "Set Data Exchange Active".
which activate the corresponding flags.
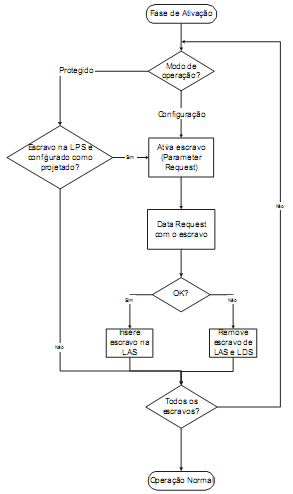
Figure 7.22: Activation phase flowchart.
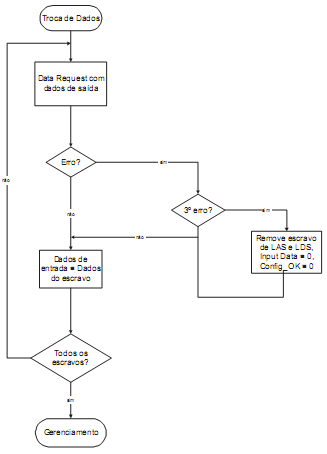
Figure 7.23: Simplified flowchart of the data exchange phase
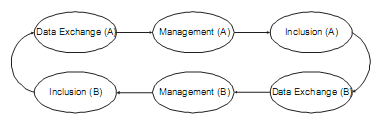
Figure 7.24: Normal operation of execution control with estn addressing
Source: SANCHES, L.B. (2004)
Expansion to Safety at Work
With AS-i Safety Work it is possible to connect safety components (safe components) such as emergency switches and safety barriers directly to the AS-i network. The goal is to add functionality related to personal and equipment safety. There is no need to change or expand the existing system. Because the safety components and the monitor work with the AS-i standard protocol.
It is only necessary to add the security components to the system. Security monitoring is not done by the network master. For this, a required component in a network with safe components is the safe monitor.
The monitor does not interfere with network frame traffic, it only monitors the traffic, using it to determine the security state. In this way, machines and plants can be set to a safe state via the safety monitor outputs. An example of a network with secure components is shown in Figure 8.1.
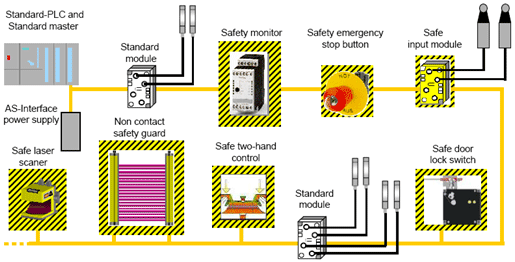
Figure 8.1: AS-i network with security components and common components.
Source: AS-International Association (2008).
AS-i limitations
AS-i was consciously built and optimized for use in applications below fieldbuses. Therefore, some capabilities of high-level fieldbuses cannot be realized in AS-i. Some limitations must be known.
- Data transmitted in AS-i is limited to 4 bits by slaves which can be exchanged every cycle. Long messages can be transmitted by splitting them into several cycles. This can be used in slow dynamic processes such as pressure or temperature (analog values).
- AS-i is strictly master-slave, with cyclic scanning by slaves. This prevents asynchronous transmission by sensors and actuators. The slaves must wait 10 ms (in the case of a network with 62 slaves) before being called again.
- Data transfer from slave to slave is only possible via the master.
- The cable length limitation is 100m without the use of repeaters. This physical limitation is due to the maintenance of other criteria such as network cycle time, type of free topology and the non-requirement of terminating resistors.
Standards and Regulations
AS-i network components and their installations must comply with the following regulations and based on their latest revisions.
- Statutory Obligations (including the Electricity Ordinance, Chapter 406);
- IEC 364: Electrical installations of buildings;
- IEC 60947-1: Low-voltage switchgear and controlgear – Part 1: General rules;
- IEC 529: Degrees of protection provided by enclosures (IP Code);
- IEC 439: Low-voltage switchgear and control gear assemblies;
- IEC 62026-1: Low-voltage switchgear and controlgear – Controller-device interfaces (CDIs);
- IEC 62026-2: Actuator sensor interface (AS-i);
- IEC 61131-2: Programmable controllers – Part 2: Equipment requirements and tests;
- IEC 61076-2-101: Connectors for electronic equipment: Part 2-101 Circular connectors (M8 & M12);
- EN 954-1: Safety of machinery. Safety related parts of control systems. General principles for design;
- CISPR 11: Industrial, scientific and medical (ISM) radio-frequency equipment – Electromagnetic disturbance characteristics – Limits and methods of measurement.
In addition to the standards and regulations mentioned above, consideration should also be given to local regulations for equipment installation, inspection and testing.
References
Bibliography
- ATAIDE, F.H. (2004). Technical Study EST-DE-0007-04 - AS-Interface, Nova Smar S/A, February.
- BECKER, R.; MÜLLER, B.; SCHIFF, A.; SCHINKE, T.; and WALKER, H. (2002). AS-Interface - The Automation Solution, AS-International Association, Germany.
- ERCEGOVAC, M.; LANG, T.; and MORENO, J.H. (2000). Introduction to Digital Systems, Bookman.
- LIAN, S.C.P. (2003). AS-i Master Bus Controller. Thesis submitted to the School of Information Technology and Electrical Engineering, The University of Queensland, June.
- MADELUNG, O.W. and KRIESEL, W.R. (1999). AS-Interface - The Automation Solution, Hanser.
- SANCHES, L.B. (2004). Technical Study EST-DE-0087-04 – AS-i Prototype, Nova Smar S/A, August.
- SILVA, W.A.C.M. (2008). Class Notes for the Higher Course in Automation Technology, CEFET-RN, Available at: http://www.cefetrn.br/~walmy/RI_A3.pdf. Last Accessed: September 16th.
- STANDARDS AUSTRALIA. (2000). Low-voltage switchgear and controlgear - controller-device interfaces (cdis), Part 2: Actuator sensor interface (AS-i).
- SYSTEM ENGINEERS (2008). General Technical Specification, Actuator Sensor Interface (AS-i). Available at: http://www.myelectrical.com/pages/tools/downloads/Accutuator Sensor Interface (AS-I) Specification.pdf. Last Access: September 16th.
- Virtual Academy of AS-International Association. Available at: http://www.as-interface.net/academy/content/sys/start/start.en.html. Last Access: November 17, 2008.
- WIKI AS-INTERFACE (2008). AS-Interface. Available at: http://en.wikipedia.org/wiki/AS-Interface. Last Access: September 13th.
Additional Information
For more information about AS-i technology, also visit the following portals.
AS-i International: http://www.as-interface.net/
AS-Interface UK Expert Alliance: http://www.as-interface.com/